Documentation.pdf - Traffic Policer 6.13.2.0 Documentation By Albo1125 Thank you Ionite for the thumbnail. This document must not be redistributed or | Course Hero

Traffic Policer (Breathalyzer, Traffic Offences, Speed Detection & more) - Page 55 - Script Modifications & Plugins - LCPDFR.com

Documentation.pdf - Traffic Policer 6.13.2.0 Documentation By Albo1125 Thank you Ionite for the thumbnail. This document must not be redistributed or | Course Hero

Adaptive tuning of network traffic policing mechanisms for DDoS attack mitigation systems - ScienceDirect
Example: Limiting Inbound Traffic Within Your Network by Configuring an Ingress Single-Rate Two-Color Policer and Configuring Multifield Classifiers | Junos OS | Juniper Networks

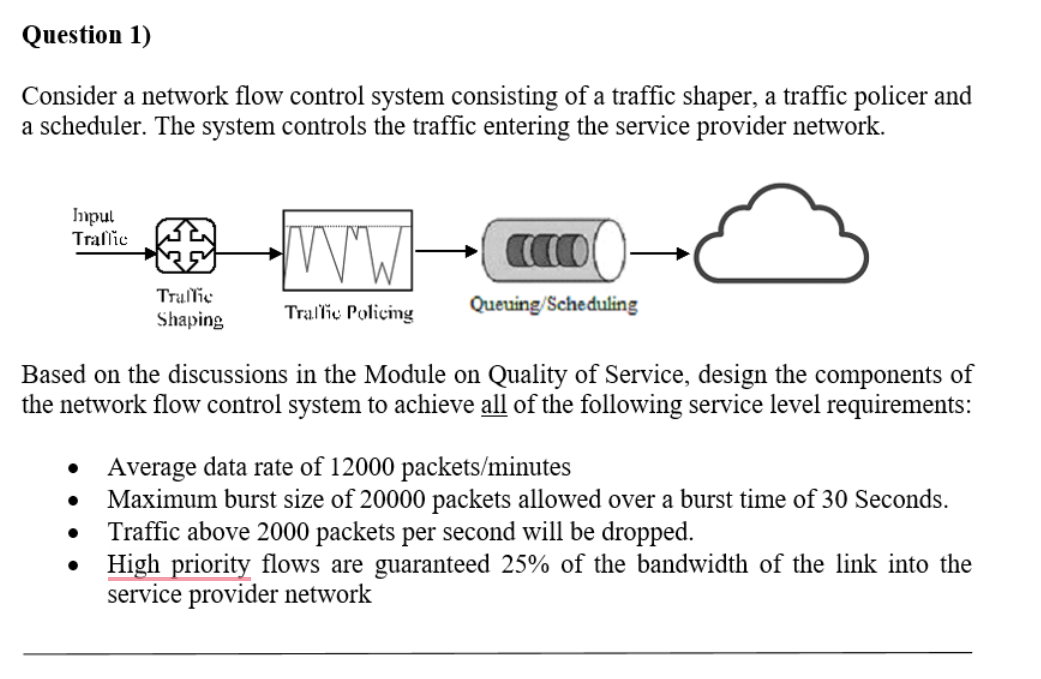
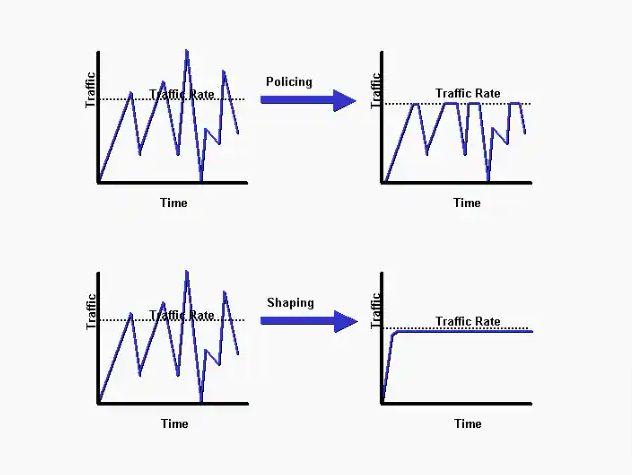
Dual Leaky Bucket Policer Traffic shaping is a complimentary technique,... | Download Scientific Diagram